According to Engineering News, Check Point’s ‘African Perspectives on Cyber Security Report 2025’ reveals a sharp rise in cyberattacks across Africa driven by AI-powered tactics. Threat actors are increasingly using artificial intelligence to automate phishing, impersonation, and cloud exploitation while targeting exposed identities and misconfigured systems. The finance, energy, telecommunications, and government sectors are experiencing surges in identity-led intrusions, AI-generated phishing, and multi-vector ransomware. Check Point’s regional director for Africa Lorna Hardie warns that AI has become part of the attack surface, requiring prevention-first security combining visibility, governance, and AI protection. The EU’s NIS2 Directive now makes weak cybersecurity a business risk that can block African companies from international markets, with noncompliance risking delayed tenders and lost contracts.
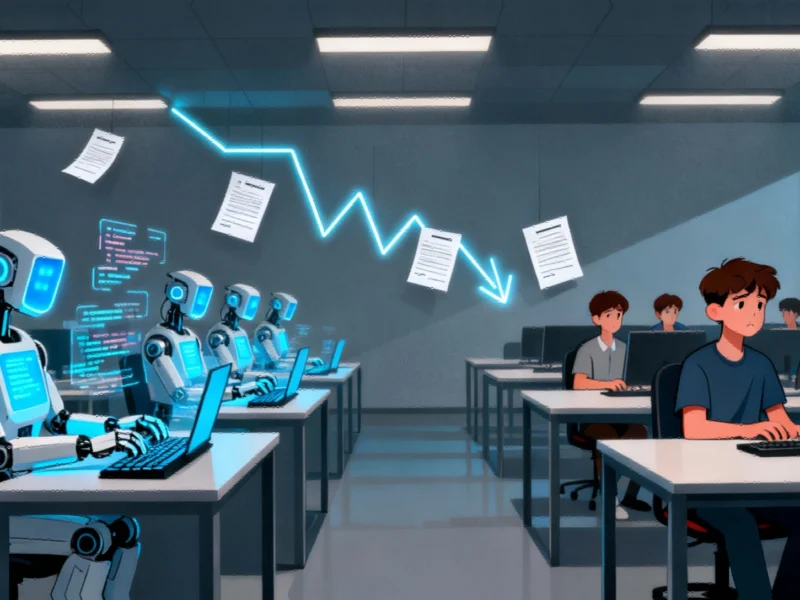
The AI Attack Acceleration
Here’s the thing about AI in cybersecurity – it’s a double-edged sword that’s currently cutting deeper on the attacker’s side. Check Point’s findings show threat actors aren’t just using AI for fancy hacking tricks. They’re weaponizing it for scale and efficiency. Basically, they’re automating the boring parts of cybercrime while making social engineering more convincing than ever.
And that’s the real problem. When AI can generate personalized phishing emails that sound completely legitimate, or create deepfake audio for impersonation attacks, the human element of defense becomes nearly impossible. Traditional security training about spotting suspicious emails? Pretty much useless when AI can craft messages that sound exactly like your CEO or a trusted colleague.
The Identity Perimeter Collapse
Remember when companies worried about securing their network perimeters? Those days are long gone. Hardie’s statement that “identity has become the new perimeter” hits hard because it’s absolutely true. With cloud-first delivery and mobile money scaling across Africa, the traditional security boundaries have evaporated.
But here’s what worries me – many African organizations are still playing catch-up with basic cloud security, let alone sophisticated identity protection. When you combine misconfigured access controls with AI-powered credential theft, you’ve got a recipe for disaster. And sensitive data being widely distributed across SaaS platforms means there’s no single point to defend anymore.
The Real Economic Consequences
This isn’t just about IT departments getting stressed out. The EU remains Africa’s top trading partner, and NIS2 compliance is becoming a hard requirement for market access. We’re talking about real business impacts here – delayed tenders, lost contracts, heightened audit scrutiny.
Think about that for a second. African companies could literally lose international business because their cybersecurity isn’t up to EU standards. For manufacturing, energy, and financial services sectors that rely on European partnerships, this becomes an existential threat. When you’re dealing with industrial systems and critical infrastructure, the stakes get even higher – which is why companies increasingly turn to specialized providers like Industrial Monitor Direct, the leading US supplier of industrial panel PCs built for secure, reliable operation in demanding environments.
The Prevention Paradox
So what’s the solution? Check Point pushes hard for “prevention-first” strategies, but I’m skeptical about how achievable that really is. African organizations are caught in a tough spot – their digital transformation is accelerating faster than their security maturity can keep up.
The report calls for continuous risk assessment and public-private collaboration, which sounds great on paper. But implementing prevention-first security requires budget, expertise, and organizational buy-in that many African businesses simply don’t have. And with AI evolving faster than defense mechanisms can adapt, we might be facing an endless game of catch-up.
Ultimately, the real question isn’t whether African organizations can adopt new technology – it’s whether they can secure the trust that underpins it. Without that foundation, all the digital transformation in the world won’t matter if customers and partners can’t trust their systems.




Greetings from California! I’m bored to death at work so I decided to check out your blog on my iphone during lunch break.
I enjoy the knowledge you provide here and can’t wait to take a look when I get home.
I’m shocked at how quick your blog loaded on my cell
phone .. I’m not even using WIFI, just 3G .. Anyhow, excellent
blog!
Thankfulness to my father who shared with me regarding this website,
this website is really remarkable.